Log with Cryptographic Proof
Every audit entry is chained and tamper-evident at the database level
HMAC Chain Integrity
Every entry is cryptographically chained to the previous using HMAC-SHA-256
Append-Only Enforcement
PostgreSQL triggers prevent updates, deletes, and truncation on audit logs
Per-Account Isolation
Independent cryptographic chains and HMAC keys for each tenant account
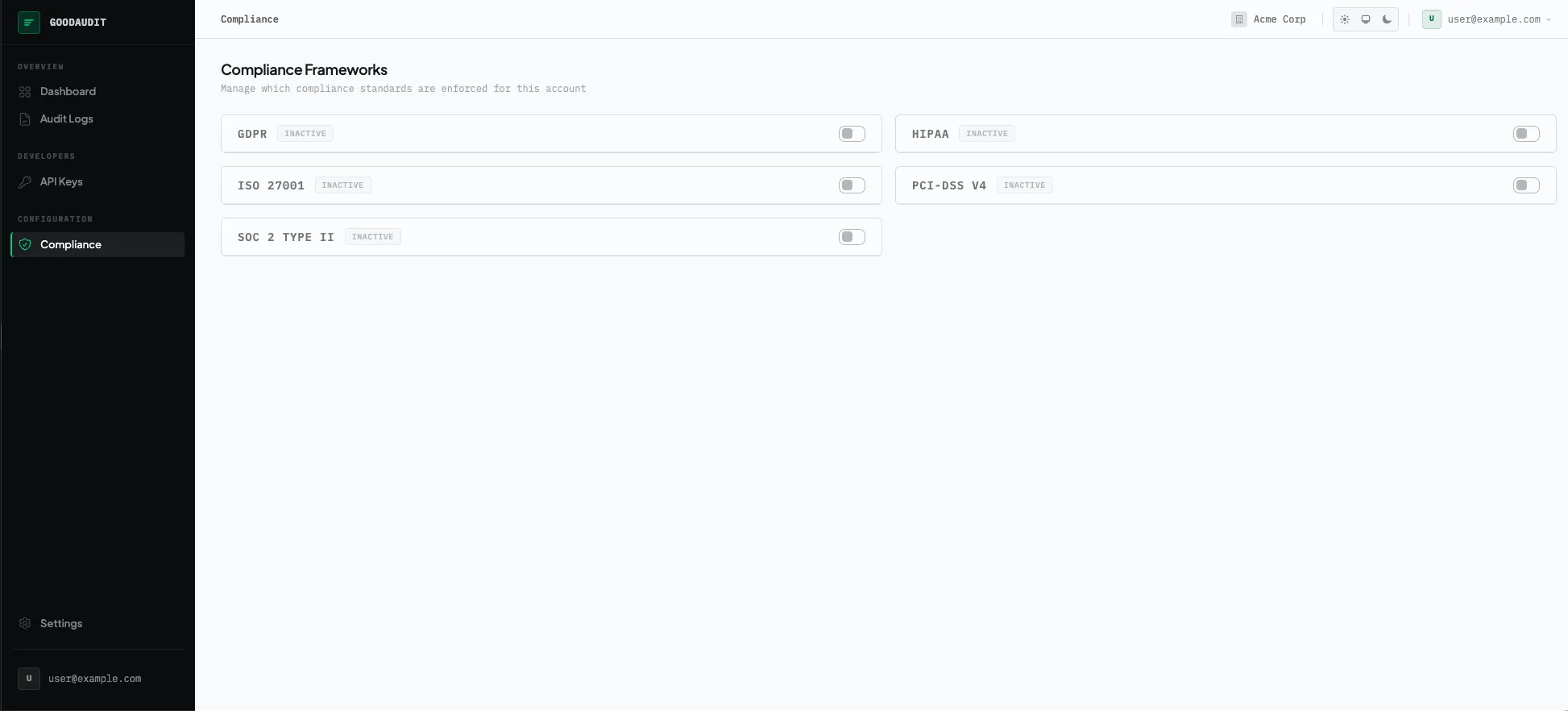
Comply Across Frameworks
Activate multiple compliance frameworks and let validation rules follow
Multi-Framework Support
Run HIPAA, SOC 2, PCI-DSS, GDPR, and ISO 27001 simultaneously
Framework-Aware Validation
Required fields enforced per framework with specific error messages
Event Taxonomies
Standard action vocabularies per framework with custom action mapping
Export Audit-Ready Evidence
Generate compliance reports your auditors will actually accept
Evidence Packages
Framework-specific report templates in JSON, CSV, and PDF formats
Chain Verification Reports
Integrity status, gap detection, and checkpoint anchor validation
Retention Policies
Framework-driven retention with automatic multi-standard conflict resolution
Related Products
More products from the GoodWay suite
Checksum.dev
Cryptographic audit logs for regulated industries
- Ed25519 cryptographic signatures on every record
- Daily Merkle tree tamper detection
- HIPAA, SOC 2, PCI-DSS, GDPR compliance reports
GoodVerify
Verify emails, phones, and addresses via API
- Email, phone, address, and social verification in one API
- DNC/TCPA compliance flags and owner enrichment
- Native MCP tools for AI agent workflows